A small business cyber security plan
October is National Cyber Security Awareness Month (NCSAM). #BeCyberSmart #CyberAware
Security is everyone’s responsibility, so whether you’re a small business, medium enterprise, SaaS provider or web agency, grab a cuppa and learn some of the ways, we at Dogsbody, recommend improving your security.
You are 9 times more likely to be a victim of fraud than burglary.
With 15 years of experience behind us we feel qualified to produce our very own small business cyber security plan.
A small business cyber security plan
Security (cyber or otherwise) all boils down to risk.
The only way to keep a system 100% safe is for it to be in a sealed room, inaccessible to people, to the internet or the outside world and even then, someone could almost certainly gain access to the room if they really wanted too.
Security isn’t just about protecting from the hacks we are aware of, it’s also about attempting to protect users from the threats which haven’t yet been discovered or made widely available.
Implementing preventative or early detection systems with the right security practices for your people, processes and IT systems should mean you become more tuned to spotting attacks or hacks, giving you a better chance to protect yourself and your business.
“100% secure is just not possible”
Technology is a constantly moving beast. So are the methods used to try to gain unauthorised access to your systems.
Your staff may be reasonably savvy about emails which impersonate companies, however as an example of the speed of technology, the Dogsbody team has seen AI now being used to fake people’s voices and scam people out of £1000’s.
Scammers are coming up with new methods to extract cash or assets from companies as fast as security experts are mitigating them.
In this article, we look at each of the three principle areas of risk for your business – People, Systems and Processes; as well as some of the things you can implement immediately to reduce your exposure.
Computer security, cybersecurity or information technology security (IT security) is the protection of computer systems from the theft of or damage to their hardware, software, or electronic data, as well as from the disruption or misdirection of the services they provide. – wikipedia.org
Risk #1- people
Humans are fallible (likely to make errors or fail). Nobody’s perfect, after all.
However there are some actions for which there are no excuses … weak passwords is one of them! Any small business cyber security plan has to put passwords at the centre of the plan.
The good news is that there are so many ways to make strong unique passwords for every single login. The video below contains a useful method for creating incredibly strong, yet memorable passwords:
Find out how easy passwords are to crack. Get scared.
Password reuse and poor passwords are unacceptable and easily preventable. We have talked before about using a password manager and 2 Factor Authentication (2FA) where available. Get to understand these tools (or talk to us!) and figure out how best to include them within your business.
Education is key
Having clear processes and good security training is another way to help make sure everyone is on the same page. Free cyber security training courses, videos and online resources are readily available from reputable sources:
- National Cyber Security Centre e-learning package: ‘Top Tips For Staff’ can be completed online, or built into your own training platform.
- Future Learn’s Introduction to Cyber Security course.
- National Cyber Security Centre exercise in a box is for businesses.
- Can you spot a #phish? Google’s free phishing quiz will test you and your employees ability to spot a fake.
Social Media – your online life
Social media allows us to find out basic details about people and companies within seconds. Using a combination of Google and Linkedin allows everyone to know who you work for.
Whilst this is great for networking, it does mean that you and your team need to be careful about what you share and and who you share it with.
If you are reading this article and rolling your eyes and think this security advice just doesn’t matter, spend three minutes watching this (brilliant) video and you might just change your mind:
Frightening huh? And hopefully thought provoking too.
Have processes in place to check when dealing with all contacts via email and phone. Are you speaking to who you think it is?.
It is also sensible to avoid giving out personal data over the phone or via insecure methods such as Slack and email.
Risk #2 – systems, servers & devices
There is something or someone trying to access your data every minute of every day.
Implementing preventative and early detection systems into your workflow may help mitigate a situation before it starts.
Devices, including servers, work laptops, home laptops, mobile phones, routers, printers, internet of things (IOT) devices (including that wifi connect light bulb) can all be used against you and your business.
Dogsbody’s #1 tip: keep your devices up-to-date
Updates for all of these devices are released regularly to address bugs, code improvements and security vulnerabilities.
If you’re not updating (patching) regularly, then you are putting yourself at a higher risk of being exploited by a known vulnerability.
Don’t be that person or company.
End of life
Be aware of software end of life (EOL). For example mobile phone hardware usually outlives its supported software meaning it’s open to new security vulnerabilities.
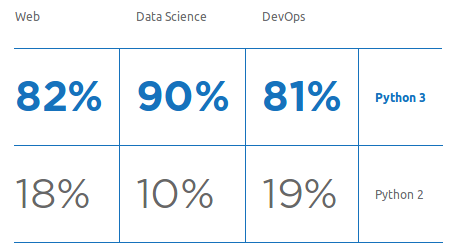
We often talk about ‘end of life’ software in our newsletter. Last month, we confirmed Python 2.7 and PHP 7.1 are going to be end of life soon. Once software is no longer supported, there are no guarantees about the security holes this software could lead too.
Restrict access
Only give access to the areas people need to do their job whether that is physical (rooms, offices), Documents (read only and write only) or devices/servers, it will make it easier to spot an intruder. Separate users means you can see who made a change giving you an audit trail should anything go amiss. Remember to remove old users.
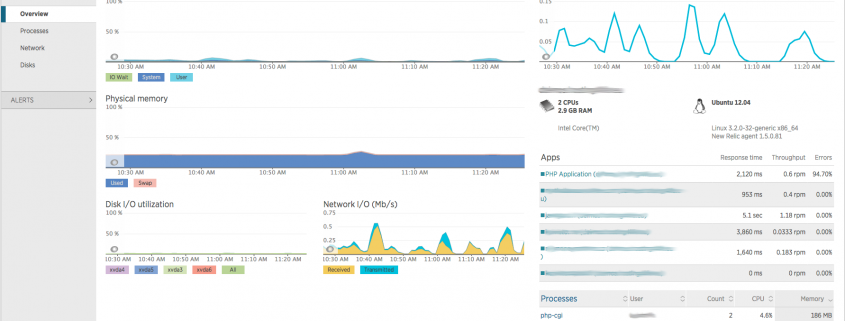
Proactive monitoring
Monitor everything: cpu, memory, disk io, disk space, ports etc. We monitor all of these metrics (and more) on behalf of 100’s of customers.
Use our free tool to monitor some of your external resources too – StatusPile allows you to build a status page of status pages.
A spike or alert across any of these metrics could mean a server is being attacked. If you respond quickly, attackers can be blocked before they cause too much damage.
Back up
We’ve written about backup strategies before. This is such a fundamental part of business.
Don’t be that company that can’t recover from an event like this:
If you lost everything where do you go?
Off site backups – simply have them, know where they are and keep them up to date.
Make sure you check them regularly. Is everything being backed up correctly? Are they actually working when you perform a restore? Is the retention policy set correctly?
It’s not good enough to set and forget – new infrastructure gets added, access codes change. Be diligent and don’t lose your business when something goes wrong.
Standardised builds
Have (documented) standard builds for servers, workstations, laptops and other network infrastructure.
Insecure configurations can allow malicious users to obtain unauthorised access, so it is important to ensure the secure configuration of all systems is set up and maintained.
If you need help, talk to us – we do this every day!
Know what you don’t know
That may sound like a crazy heading – but we really mean it. If you don’t test your infrastructure regularly, you don’t know what’s really going on. Involve a third party, get an expert to ethically hack into your systems. This process is of course known as penetration testing.
Penetration tests take many different forms. Testing once a year is a step in the right direction, however infrastructure changes regularly and rightly so, patches must be applied and users added and removed, its a constantly moving beast, so it makes sense to have regular penetration tests. Whilst they give you peace of mind – they will also give your customers peace of mind too.
Protect your email
Make it harder for impersonators to send spam which looks like it comes from your business by setting up your email correctly.
Public wifi is a notorious place for hackers to lurk
Know the risks of public wifi.
Usually it’s free and often, it’s not secure. Avoid visiting sensitive sites such as banks, accounts packages, work ticketing systems when connected.
Company VPN’s can be used if you need to do this regularly. Personal VPN applications are good too for personal browsing.
Risk #3 – processes
Processes have been intertwined within the previous two sections. We’ve discussed standardised builds, communications. device and social media policies.
It’s now time to mop up some of the areas we’ve not yet mentioned.
How would you respond to an emergency if your digital channels were down?
If and when something does go wrong have you considered how you would communicate with your customers?
Host your status page on a completely separate hosting provider to all your other business activities and remember, to make the password accessible for when you are offline.
Status pages are for facts. Do not speculate or discuss issues that have not been confirmed.
Crisis communications is a consideration for all businesses.
Documentation
You rarely hear people talking about the joys of documentation, however it’s a necessary evil of business and absolutely could be your saviour one day.
Here at Dogsbody, we do it as a matter of course. Without shared documentation, IT systems are left exposed. employees leave, employees get sick. It’s essential others can understand how your IT infrastructure works.
Server build documentation is the recipe for your servers. If a server was down and the only way to recover it was to rebuild it – would you know how to? Is it clear how it was set up … who had access … and how the operating system was configured?
Having a build guide document in place means anyone can pick it up and get it back online quickly.
Subscribe for service updates
Subscribe to your providers service updates, notifications, emails and/or RSS feeds, monitor Status pages, hang out on tech forums – as a Linux managed server provider, our team are always reading blogs, security updates and notices – its just part of the day job.
The Government National Cyber security centre release weekly threat reports as well as advice on all security topics.
___________
That wraps up our small business cyber security plan. We hope it makes you think about how your business approaches online security.
If we can help answer any questions, please don’t hesitate to get in touch.








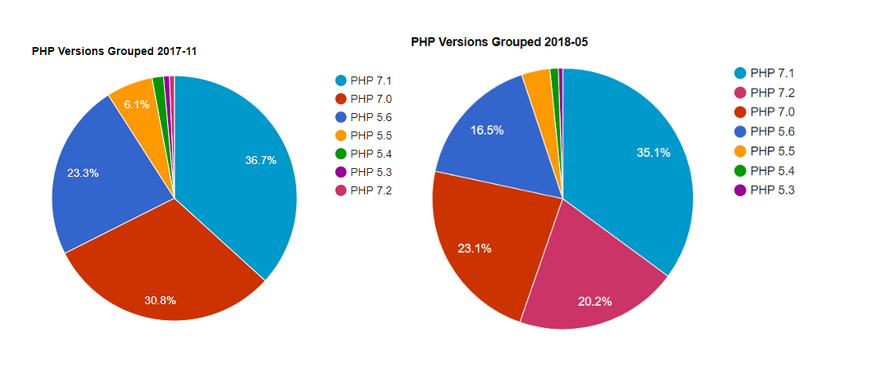 Upgrade from PHP 7.1 before the 1st December 2019.
Upgrade from PHP 7.1 before the 1st December 2019.